
Emerging IoT hacking techniques are constantly evolving, pushing beyond simple password cracking into more sophisticated and insidious territory. As the number of connected devices skyrockets into the billions, they create a vast and vulnerable attack surface that cybercriminals are eager to exploit.
From smart homes and wearable tech to industrial sensors and critical infrastructure, the very connectivity that makes the Internet of Things (IoT) so powerful also makes it a prime target. Understanding these new IoT threats is the first and most critical step in developing a robust defense.
This guide will delve into the latest methods attackers are using and provide a actionable framework to significantly strengthen your IoT security posture.
The Evolving Threat: Understanding Emerging IoT Hacking Techniques
The days of attackers only relying on default passwords are not over, but their arsenal has expanded dramatically. Modern IoT hacking techniques are more automated, stealthy, and damaging.
1. AI-Powered Vulnerability Discovery
Cybercriminals are now using artificial intelligence (AI) and machine learning to automate the discovery of vulnerabilities. Instead of manually testing devices, AI algorithms can scan millions of devices simultaneously, analyzing responses to identify weaknesses in firmware, network protocols, and web interfaces far more quickly than any human could. This allows attackers to weaponize new vulnerabilities at an unprecedented scale and speed, often before manufacturers are even aware the flaw exists.
2. Side-Channel Attacks
This is a particularly clever and difficult-to-detect class of attack. Instead of targeting software directly, side-channel attacks exploit physical artifacts of a device’s operation. By analyzing patterns in power consumption, electromagnetic leaks, or even subtle sounds emitted by a device’s components, a sophisticated attacker can deduce sensitive information like encryption keys. This technique is a significant threat to critical IoT systems where physical access might be possible, as it can bypass traditional software-based security entirely.
3. Ransomware for IoT and Operational Technology (OT)
Ransomware has moved beyond encrypting files on computers. A devastating emerging IoT hacking technique involves targeting smart devices and industrial control systems. Imagine a smart thermostat in a large building being locked by ransomware in the dead of winter, or the control systems of a manufacturing plant being held hostage.
Attackers can demand a ransom to restore functionality, causing massive operational disruption and financial loss. Unlike a computer, many of these devices cannot be easily restored from a backup, giving attackers significant leverage.
4. Botnets for Cryptojacking and DDoS 2.0
While botnets like Mirai are well-known, their evolution continues. Modern botnets are now often used for “cryptojacking”— secretly using the processing power of thousands of compromised IoT devices to mine cryptocurrency, slowing devices down and increasing energy costs for the owner.
Furthermore, Distributed Denial-of-Service (DDoS) attacks have become more sophisticated. Instead of just flooding a target with traffic, attackers now use IoT botnets to launch more targeted application-layer attacks that can cripple online services while using less bandwidth and being harder to mitigate.
Emerging IoT Threats & Strategic Defenses
| Hacking Technique | What It Is | Target Impact | Primary Defense Strategy |
| AI-Powered Discovery | Using ML to find 0-day flaws. | Massive, automated device takeovers. | Zero-Trust Network: Isolate IoT traffic. |
| Side-Channel Attacks | Monitoring physical artifacts (power/heat). | Theft of encryption keys and data. | Physical Security: Hardware-level shielding. |
| IoT Ransomware | Locking OT/Smart building controls. | Operational paralysis & financial loss. | Immutable Backups: Regular firmware snapshots. |
| Cryptojacking | Stealing CPU power to mine crypto. | Device lag and high energy bills. | Egress Monitoring: Block unusual outbound traffic. |
| DDoS 2.0 | Targeted application-layer floods. | Crippling online services & downtime. | Traffic Scrubbing: Use advanced firewalls. |
Building Your Digital Fortress: How to Stay Protected
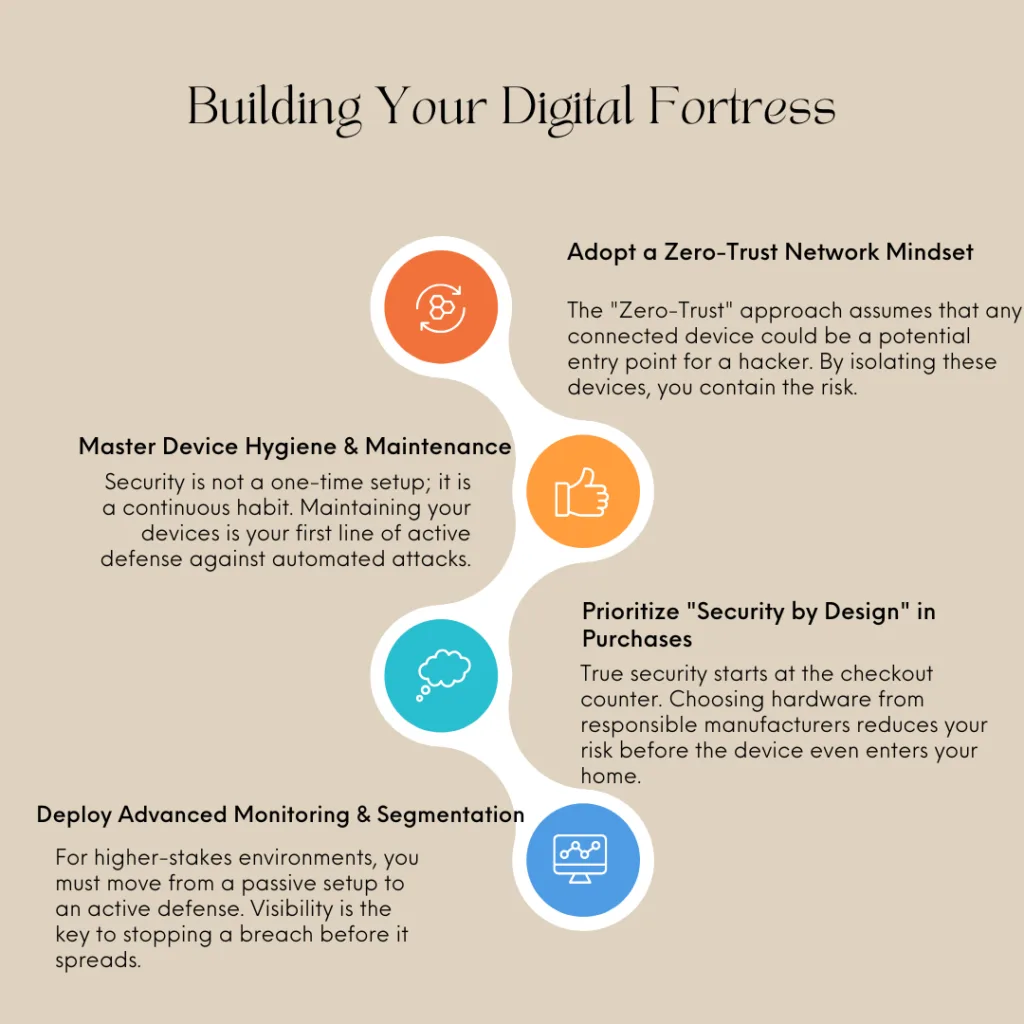
In the face of these advanced IoT threats, a proactive and layered security strategy is non-negotiable. Here’s how to build a resilient defense.
1. Adopt a Zero-Trust Mindset for Your Network
The most effective single step you can take is to segment your network. Do not let your smart lightbulbs, security cameras, and other IoT devices reside on the same Wi-Fi network as your personal computers, phones, and sensitive data.
- Action: Create a separate “Guest” network specifically for all your IoT devices. Most modern routers have this feature. This simple step ensures that if a smart device is compromised, the attacker cannot easily pivot to your more sensitive systems.
2. Rigorous Device Management and Hygiene
Your IoT security posture depends heavily on basic, consistent maintenance.
- Change Default Credentials Immediately: This remains the number one cause of IoT compromises. Always set a unique, strong password during initial setup.
- Disable Unnecessary Features: If a device has features you don’t use—like remote access via UPnP (Universal Plug and Play)—disable them. Every enabled service is a potential entry point.
- Commit to Firmware Updates: Enable automatic updates if available. If not, regularly check the manufacturer’s website for firmware patches and apply them promptly. This is your primary defense against known vulnerabilities.
3. Prioritize Security in Your Purchasing Decisions
The best defense is a device that is secure by design. As a consumer or a business, you have the power to influence the market by supporting responsible manufacturers.
- Research Before You Buy: Look for brands with a strong reputation for security and a clear commitment to providing regular, long-term security support for their products.
- Look for Certifications: Check if the device has undergone independent security testing or carries relevant certifications.
- Vet Vendor Policies: Understand the vendor’s vulnerability disclosure policy. Do they have a clear channel for researchers to report flaws?
4. Deploy Advanced Monitoring and Segmentation
For businesses and highly security-conscious individuals, more advanced measures are warranted.
- Network Monitoring: Use network monitoring tools to keep an eye on the traffic flowing to and from your IoT devices. Unusual data transfers or communication with unknown servers in foreign countries can be a red flag.
- Formal Segmentation: In enterprise environments, use firewalls to create strict rules controlling how IoT devices can communicate, both with the internet and with other internal systems.
Conclusion: Vigilance in a Connected World
The landscape of emerging IoT hacking techniques is dynamic and challenging, but it is not undefeatable. By moving beyond a passive setup-and-forget mentality and embracing an active, layered security strategy, you can dramatically reduce your risk.
Understanding the threats—from AI-powered scanning to operational ransomware—empowers you to make informed decisions. Strengthening your IoT security posture through network segmentation, diligent device management, and smart purchasing creates a resilient environment where you can safely enjoy the immense benefits of a connected world without falling victim to its inherent dangers.
Frequently Asked Questions (FAQs)
1. My IoT device is from a reputable brand. Is it still vulnerable?
Absolutely. Even reputable manufacturers can ship devices with software vulnerabilities that are discovered after release. No software is perfectly secure. The brand’s reputation is often reflected in how quickly and transparently they address and patch these vulnerabilities when they are found, not in the absence of flaws altogether.
2. What is the single most important thing I can do to protect my IoT devices at home?
Without a doubt, the most impactful action is to place all your IoT devices on a separate Wi-Fi network (a guest network). This simple, free step isolates your vulnerable devices from your computers and phones, containing a potential breach and preventing attackers from accessing your most sensitive data.
3. How can I tell if one of my IoT devices has already been hacked?
Signs can be subtle but include a noticeable decrease in device performance or internet speed (from cryptojacking or botnet activity), unexpected data usage on your bill, the device behaving erratically on its own (e.g., a camera moving), or inability to log in with your credentials because the password was changed by an attacker.

