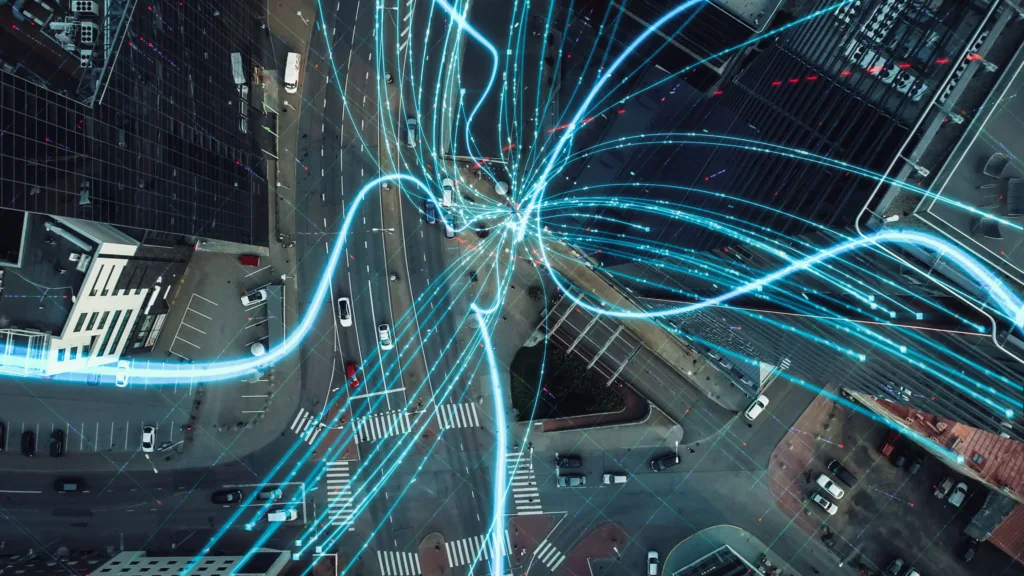
Cybersecurity Challenges in the Era of 5G are becoming one of the most pressing concerns for governments, corporations, and individuals alike. The rollout of fifth-generation (5G) wireless technology promises a revolution—a world of unprecedented speed, ultra-low latency, and massive device connectivity. It is the foundational backbone for smart cities, autonomous vehicles, advanced telemedicine, and the ever-expanding Internet of Things (IoT).
However, this seismic leap in technological capability is a double-edged sword. While it unlocks incredible potential, it simultaneously introduces a new and complex landscape of vulnerabilities, creating a broader and more dangerous attack surface than ever before. Understanding these cybersecurity challenges is the first step toward building the resilient digital ecosystems of tomorrow.
Table of Contents
The Expanded Attack Surface: A Hacker’s Playground
The most significant shift that 5G brings is the dramatic expansion of the digital attack surface. In the 4G era, the primary connected devices were smartphones and computers. 5G is designed to connect everything—from critical infrastructure like power grids and water systems to everyday objects like home appliances, medical devices, and industrial sensors.
This hyper-connectivity creates millions of new potential entry points for cybercriminals. Many of these IoT devices are built with minimal, if any, built-in security features. They are often “set-and-forget” devices with weak default passwords and unpatched software vulnerabilities.
A compromised smart thermostat might seem insignificant, but it can serve as a foothold within a network, allowing attackers to move laterally to target more critical systems.
This vast web of poorly secured devices provides a powerful botnet army for launching large-scale Distributed Denial-of-Service (DDoS) attacks that can cripple essential online services. Therefore, the sheer scale of connectivity is, in itself, a monumental 5G network security challenge.
Virtualization and Software Vulnerabilities
At the heart of 5G’s architecture is a move away from traditional, hardware-based network components toward Network Function Virtualization (NFV) and Software-Defined Networking (SDN). This shift is what makes 5G so agile and efficient, allowing network resources to be allocated dynamically.
However, it also replaces dedicated physical hardware with software running on commercial off-the-shelf servers.
This introduces a new class of risks. Software is inherently more vulnerable to bugs and exploits than proprietary hardware. A single vulnerability in the virtualized core network could potentially affect the entire system, unlike in legacy systems where a fault was often isolated to a specific piece of equipment.
Furthermore, the increased reliance on common software and standardized protocols means that if a hacker discovers a flaw, it could be exploited across multiple network providers simultaneously. Securing this complex virtualized environment requires a new approach to 5G network security, one that focuses on continuous monitoring, patch management, and software integrity checks.
Supply Chain Threats and Trust Issues
The global nature of the 5G supply chain presents another profound layer of cybersecurity challenges. Network equipment and components are manufactured by a diverse array of vendors across different countries, each with their own security standards and potential ties to nation-states.
The concern is that a malicious actor could compromise equipment during the manufacturing or distribution process, embedding hidden backdoors, malicious code, or vulnerabilities that could be activated remotely years later.
This threat is not merely theoretical. A compromised component from an untrustworthy vendor could allow a hostile state to eavesdrop on sensitive communications, disrupt critical services during a geopolitical crisis, or steal intellectual property on an industrial scale.
Mitigating this risk requires rigorous vetting of suppliers, comprehensive hardware and software audits, and a strategic shift towards diversifying the supply chain to avoid over-reliance on any single vendor. Building trust in the entire ecosystem is a non-negotiable aspect of modern security protocols.
The Critical Need for Advanced Security Protocols
Addressing these multifaceted cybersecurity challenges demands a paradigm shift in security protocols. The legacy security models, often perimeter-based and reactive, are ill-suited for the dynamic and decentralized nature of 5G networks.
The industry must adopt a “zero-trust” architecture, which operates on the principle of “never trust, always verify.” In a zero-trust model, no device or user, whether inside or outside the network perimeter, is granted automatic access. Every access request must be authenticated, authorized, and encrypted before any connection is allowed.
Furthermore, encryption must be end-to-end and ubiquitous. While 5G standards include improved encryption over the air interface, data must remain protected as it travels through the entire network, including the virtualized core.
The integration of Artificial Intelligence (AI) and Machine Learning (ML) is also becoming essential. These technologies can analyze network traffic in real-time, identifying subtle patterns and anomalies that signal a sophisticated cyber-attack long before traditional signature-based systems would detect a threat. Proactive defense, powered by AI, is the key to managing the scale and speed of threats in the 5G world.
Conclusion
The dawn of the 5G era is undeniably exciting, offering a future brimming with innovation and connectivity. However, this bright future is shadowed by significant and evolving cybersecurity challenges. The expanded attack surface, software-centric vulnerabilities, and complex supply chain risks create a threat landscape that is both broader and deeper than anything we have faced before. Successfully navigating this new era requires a concerted effort from network providers, device manufacturers, policymakers, and end-users. By prioritizing robust, intelligent, and adaptive security protocols from the ground up, we can harness the full power of 5G while building a resilient and secure foundation for the future.
Frequently Asked Questions (FAQs)
1. Is 5G itself inherently insecure?
No, the 5G standard was designed with several security improvements over 4G, such as stronger encryption over the air and enhanced subscriber identity protection. The cybersecurity challenges arise not from the standard itself, but from its implementation, the vastly expanded network of connected devices, and its new software-based architecture, which collectively create a larger attack surface.
2. How does 5G make my personal devices more vulnerable?
The primary risk to personal devices comes from the Internet of Things (IoT) ecosystem. As your home and life become more connected with smart devices (cameras, speakers, appliances) on the 5G network, each device is a potential entry point. If these devices have weak security, they can be hacked to steal your data, spy on you, or be enlisted in a botnet. Practicing good 5G network security at home, like using strong passwords and a secure Wi-Fi network, is crucial.
3. What is the single biggest cybersecurity challenge introduced by 5G?
While there are many, the dramatic expansion of the attack surface is often considered the most fundamental challenge. Connecting billions of new, often poorly secured, devices to a high-speed network creates an unprecedented number of targets for cybercriminals, making it extremely difficult to monitor and defend every potential point of entry.


