
For decades, enterprise security followed a simple mental model. Build a strong perimeter around your network, keep the bad guys out, and trust everyone who makes it inside.
And honestly, this “castle-and-moat” approach worked tolerably well when employees sat at desks inside corporate offices, accessing resources on on-premises servers.
But if you look at how businesses operate today, that model starts to feel outdated almost immediately.
People are working from home, cafés, and airports, accessing company data from coffee shops in five time zones. Applications are spread across AWS, Azure, Google Cloud, and dozens of SaaS platforms. Contractors and third-party tools are deeply embedded into workflows.
A single compromised credential can grant an attacker broad access to sensitive systems because, once they’re “inside,” traditional security trusts them completely.
Also Read:- How to Use Copilot in Software Testing
What Is Zero Trust Architecture?
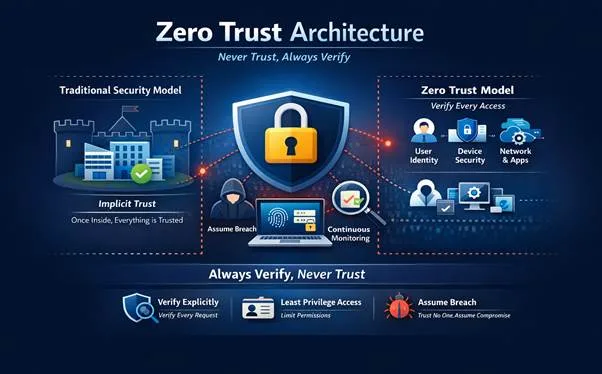
Zero Trust Architecture (ZTA) is a cybersecurity framework that eliminates the concept of implicit trust from an organization’s network. The concept, introduced by Forrester Research analyst John Kindervag in 2010 and later codified by NIST Special Publication 800-207, is built on one central principle:
Never trust. Always verify.
In a Zero Trust model, every user, device, application, and network flow is considered untrusted until explicitly authenticated, authorized, and continuously validated.
In practical terms, this means:
- Every user must prove their identity
- Every device must be validated
- Every request must be authenticated and authorized
- And this doesn’t happen once, it happens continuously
Even if the request is coming from inside your network.
So how does Zero Trust actually work?
Unlike traditional models that assume authenticity within a network boundary, Zero Trust assumes potential compromise can exist everywhere- both external and internal.
It looks at:
- Who is requesting access
- From which device
- From which location
- Under what conditions
And then decides, in real time, whether access should be granted. Even after access is granted, it is limited, monitored, and continuously revalidated
What are the core principles behind Zero Trust?
There are three foundational principles that define how Zero Trust operates.
1.) Verify explicitly- Nothing is assumed. Authenticate and authorize based on all data points: user identity, device posture, location, role, workload, and risk signals.
2.) Use least privilege access- Enforce just-in-time and just-enough-access (JIT/JEA) to restrict user and application permissions to their minimum necessary scope.
3.) Assume breach- Design systems as if attackers are already inside, focusing on detection, containment, and minimizing blast radius.
Why Are Companies Adopting Zero Trust, and Why Now?
Zero Trust is not a new idea. But the pace of adoption has accelerated dramatically in the last five years. Several converging forces have made it not just attractive, but urgent.
Reason 1: The remote work revolution made perimeters obsolete
When employees started working from everywhere, the traditional network boundary became irrelevant. Employees are now accessing corporate resources from home networks, personal devices, and public Wi-Fi.
The corporate perimeter- the firewall, the VPN, the DMZ, became a fiction. Zero Trust’s model, which assumes all networks are hostile and validates every connection independently, was purpose-built for this environment.
Reason 2: Cloud adoption shattered the traditional network
When applications live in Azure, Salesforce, GitHub, and dozens of other SaaS platforms, there is no longer a single network to protect. Data flows between cloud providers, CDNs, mobile clients, and on-premises systems in a constant, complex mesh.
Zero Trust treats every interaction in this mesh, regardless of where it originates, with equal scrutiny.
Reason 3: Insider threats are a growing and underestimated risk
Not all threats come from outside.Traditional perimeter security is defenseless against threats that originate inside the organization , whether from a disgruntled employee, a contractor with excessive privileges, or a legitimate user whose credentials have been stolen.
Zero Trust’s principle of least privilege and continuous verification means that even a compromised internal account has minimal ability to cause damage. Access is scoped tightly, and anomalous behavior triggers re-verification or revocation.
Reason 4: Ransomware and lateral movement
Modern ransomware attacks rarely strike immediately after entry. Attackers typically spend weeks or months moving laterally through a network, escalating privileges, identifying valuable systems, and planting persistence mechanisms, before triggering their payload.
Zero Trust’s micro-segmentation and least-privilege access dramatically limit this lateral movement. Even if an attacker compromises one endpoint, they cannot freely traverse the rest of the network.
Reason 5: Regulatory pressure and compliance requirements
Frameworks including NIST 800-207, the U.S. federal government’s Executive Order 14028 (which mandated Zero Trust adoption across federal agencies), GDPR, HIPAA, and PCI-DSS increasingly align with Zero Trust principles.
Organizations operating in regulated industries including finance, healthcare, government contracting, are finding that adopting Zero Trust simultaneously satisfies multiple compliance mandates while strengthening their actual security posture.
Reason 6: Supply chain and third-party risk
The SolarWinds and Log4Shell incidents demonstrated that sophisticated attackers can infiltrate organizations through trusted third-party software and vendors.
Zero Trust treats even trusted vendors and software with skepticism, requiring explicit verification before granting access to internal resources. It reduces the blast radius when a supply chain component is compromised.
How Zero Trust Is Implemented
Implementing Zero Trust is not a single product purchase or a weekend migration, but an ongoing organizational transformation. Typical deployments progress through these phases:
- Identity and access management (IAM): Deploy strong MFA, single sign-on (SSO), and continuous authentication. Identity becomes the new perimeter.
- Device trust: Enroll all endpoints in a mobile device management (MDM) or endpoint detection and response (EDR) solution. Only compliant devices get access.
- Micro-segmentation: Replace flat network architectures with granular zones. Applications talk to each other only when explicitly permitted.
- Policy engine and enforcement: Implement a policy decision point (PDP) that evaluates contextual signals- user role, device health, location, time of day, and grants or denies access dynamically.
- Monitoring and analytics: Continuous telemetry, SIEM integration, and behavioral analytics create a feedback loop. Anomalies trigger automated responses.
The Path Forward
The adoption curve for Zero Trust has inflected sharply upward. According to market research, global spending on Zero Trust security solutions exceeded $35 billion in 2024 and is projected to surpass $90 billion by 2030. Governments, Fortune 500 enterprises, mid-market companies, and even startups are investing in Zero Trust capabilities to operate safely in an interconnected digital economy.
So the question is- how much of your business today is still running on trust that hasn’t been verified?
Also Read:- Beyond the MVP: How to Prioritize Features for Your Next Product Iteration
FAQs
1. Does Zero Trust eliminate the need for VPNs completely?
Not necessarily. Some organizations replace VPNs with Zero Trust Network Access (ZTNA), while others use a hybrid model during transition, depending on security maturity and infrastructure constraints.
2. What is the biggest mistake companies make when adopting Zero Trust?
Treating Zero Trust as a product instead of a strategy. Many organizations invest in tools without aligning identity, policy, and architecture, which leads to fragmented and ineffective implementations.
3. Can small and mid-sized businesses realistically adopt Zero Trust?
Yes. SMBs can start with identity-first approaches like MFA, device compliance, and access control policies. Full-scale implementation may be complex, but foundational steps are highly achievable.
4. How do you measure the success of a Zero Trust implementation?
Success is measured through reduced attack surface, fewer lateral movement incidents, improved access visibility, and faster detection and response times rather than just tool deployment or compliance checklists.
